定位主机
有安全设备
直接根据告警的内网ip一键定位
无安全设备
那通报给的ip包是公网统一出口ip,就得一台台电脑排查了
排查思路
查看外联,定位pid->tasklist定位进程名->找路径->删除->持久化排查
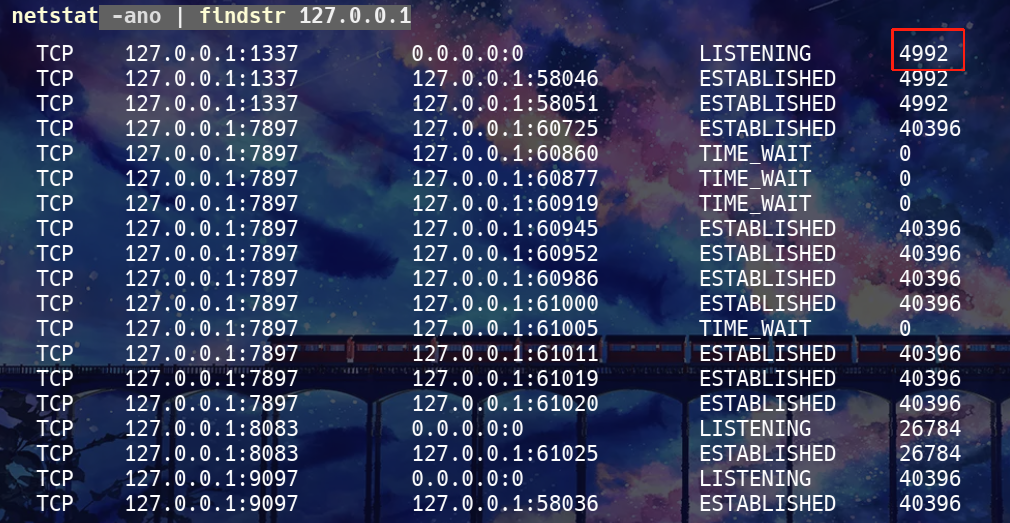
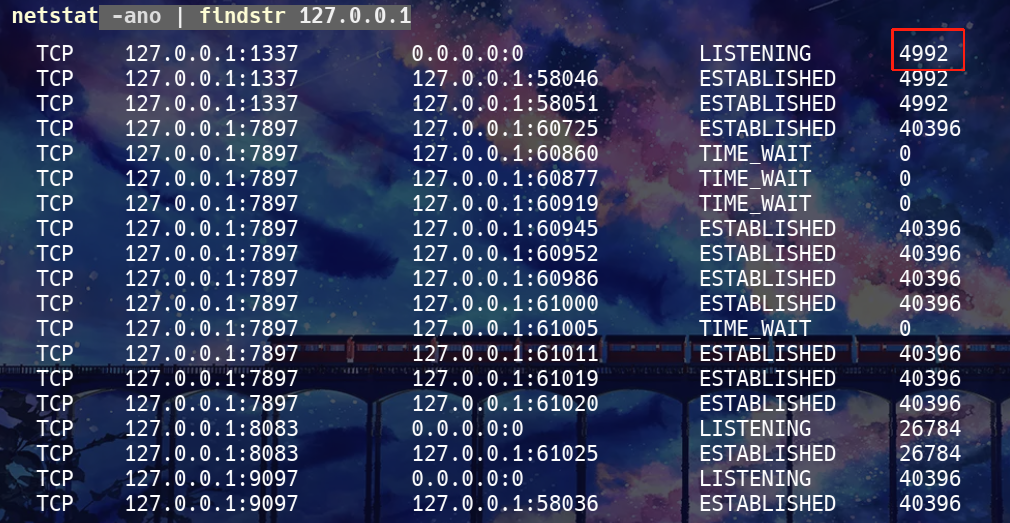
查看外联,定位pid
1
| netstat -ano | findstr ip
|
红框那一列就是pid
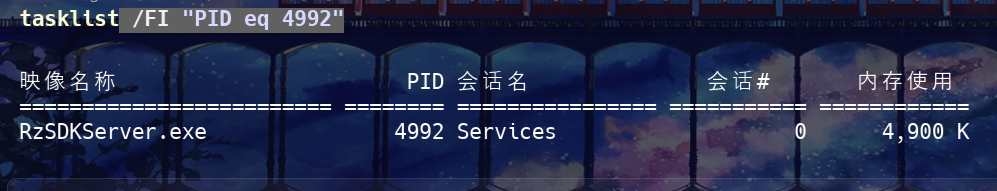
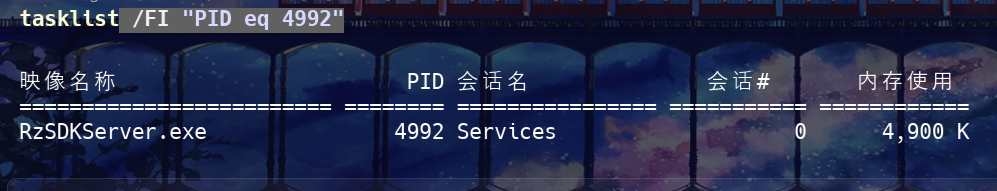
tasklist定位进程名
1
| tasklist /FI "PID eq 4992"
|
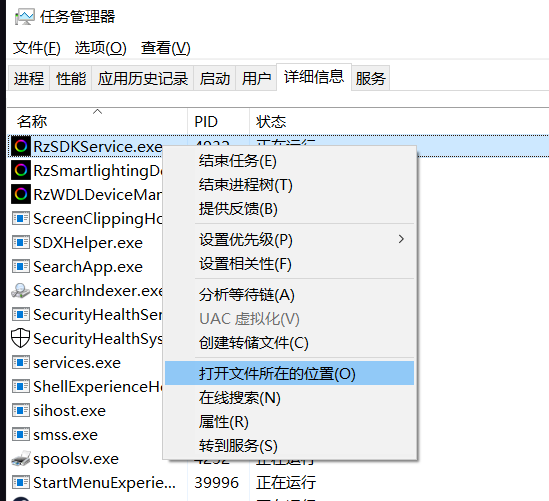
找路径
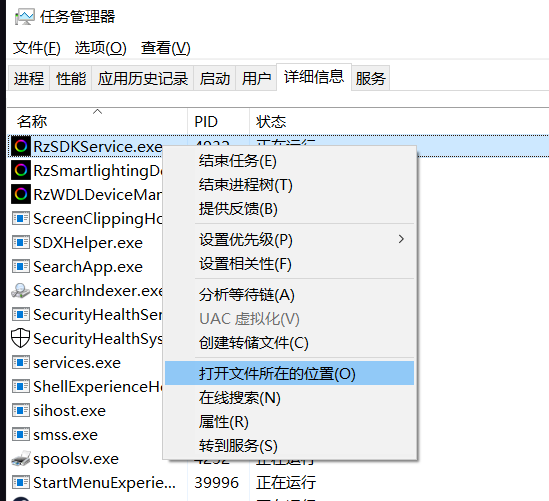
任务管理器
可以直接打开任务管理器找,在详细信息那里,找到后右键找路径
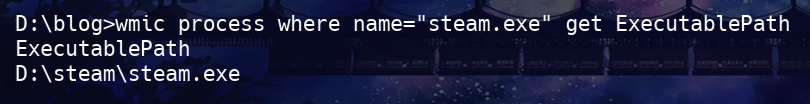
命令行
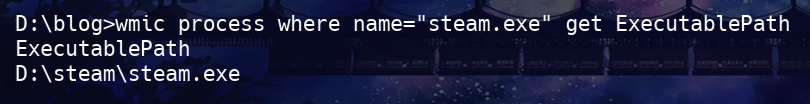
cmd
1
| wmic process where name="steam.exe" get ExecutablePath
|
或者
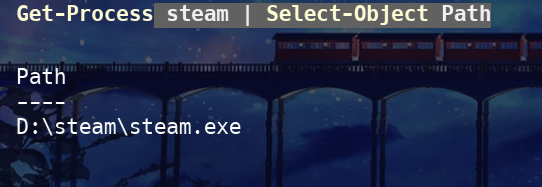
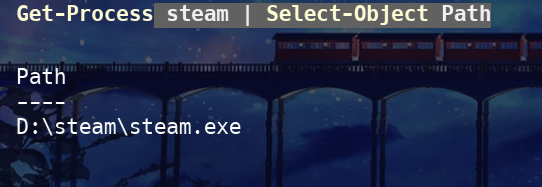
powershell
1
| Get-Process steam | Select-Object Pat
|
持久化排查
注册表启动项
木马常用注册表自启动位置:
| 类型 |
注册表路径 |
描述 |
| 当前用户启动 |
HKCU\Software\Microsoft\Windows\CurrentVersion\Run |
用户登录自动启动 |
| 当前用户 RunOnce |
HKCU\Software\Microsoft\Windows\CurrentVersion\RunOnce |
用户下次登录时启动一次 |
| 全局启动 |
HKLM\Software\Microsoft\Windows\CurrentVersion\Run |
所有用户登录自动启动 |
| 系统登录 |
HKLM\Software\Microsoft\Windows NT\CurrentVersion\Winlogon\Userinit |
登录时执行程序 |
| 系统登录 Shell |
HKLM\Software\Microsoft\Windows NT\CurrentVersion\Winlogon\Shell |
登录时执行程序 |
实例操作:
假设木马路径是
cmd
排查当前用户开机自启
1
| reg query "HKCU\Software\Microsoft\Windows\CurrentVersion\RunOnce" /v *
|
排查当前用户下一次登录自启
1
| reg query "HKCU\Software\Microsoft\Windows\CurrentVersion\RunOnce" /v *
|
排查所有用户登录自启
1
| reg query "HKLM\Software\Microsoft\Windows\CurrentVersion\Run" /v *
|
排查系统登录时执行程序
1
| reg query "HKLM\Software\Microsoft\Windows NT\CurrentVersion\Winlogon" /v Userinit
|
1
| reg query "HKLM\Software\Microsoft\Windows NT\CurrentVersion\Winlogon" /v Shell
|
powershell
$malware填木马路径
1
| $malware="D:\steam\steam.exe"; $paths=@("HKCU:\Software\Microsoft\Windows\CurrentVersion\Run","HKCU:\Software\Microsoft\Windows\CurrentVersion\RunOnce","HKLM:\Software\Microsoft\Windows\CurrentVersion\Run"); foreach($p in $paths){if(Test-Path $p){Get-ItemProperty -Path $p|ForEach-Object{$_.PSObject.Properties|ForEach-Object{if($_.Value -like "*$malware*"){Write-Output "注册表自启动: $p -> $($_.Name) = $($_.Value)"}}}}}; $userinit=Get-ItemProperty -Path "HKLM:\Software\Microsoft\Windows NT\CurrentVersion\Winlogon" -Name Userinit; if($userinit.Userinit -like "*$malware*"){Write-Output "Userinit 包含木马: $($userinit.Userinit)"}; $shell=Get-ItemProperty -Path "HKLM:\Software\Microsoft\Windows NT\CurrentVersion\Winlogon" -Name Shell; if($shell.Shell -like "*$malware*"){Write-Output "Shell 包含木马: $($shell.Shell)"}
|
计划任务
cmd
1
| schtasks /query /fo LIST /v
|
powershell
1
| $malware="D:\steam\steam.exe"; schtasks /query /fo LIST /v | ForEach-Object { if ($_ -match [regex]::Escape($malware)) { Write-Output "发现木马计划任务: $_" } }
|
启动目录
cmd
1
2
| dir "%APPDATA%\Microsoft\Windows\Start Menu\Programs\Startup" /s
dir "C:\ProgramData\Microsoft\Windows\Start Menu\Programs\Startup" /s
|
powershell
1
2
3
4
5
| $startupUser = "$env:APPDATA\Microsoft\Windows\Start Menu\Programs\Startup"
$startupAll = "C:\ProgramData\Microsoft\Windows\Start Menu\Programs\Startup"
Get-ChildItem $startupUser -Recurse | ForEach-Object { if ($_.FullName -like "*$malware*") { Write-Output "用户启动目录: $($_.FullName)" } }
Get-ChildItem $startupAll -Recurse | ForEach-Object { if ($_.FullName -like "*$malware*") { Write-Output "全局启动目录: $($_.FullName)" } }
|
系统服务
cmd
1
2
| sc query type= service state= all
sc qc <服务名>
|
在第二个命令的输出里查 PathName 是否包含木马路径
powershell
1
| $malware="D:\steam\steam.exe"; Get-WmiObject win32_service | ForEach-Object { if ($_.PathName -like "*$malware*") { Write-Output "发现木马服务: $($_.Name) -> $($_.PathName)" } }
|
WMI 持久化
1
| Get-WmiObject -Namespace root\subscription -Class __EventConsumer | ForEach-Object { if ($_.CommandLine -like "*$malware*") { Write-Output "WMI EventConsumer 包含木马: $($_.Name)" } }
|
1
| Get-WmiObject -Namespace root\subscription -Class __EventFilter | ForEach-Object { if ($_.Query -like "*$malware*") { Write-Output "WMI EventFilter 包含木马: $($_.Name)" } }
|
1
| Get-WmiObject -Namespace root\subscription -Class __FilterToConsumerBinding | ForEach-Object { if ($_.Consumer -like "*$malware*" -or $_.Filter -like "*$malware*") { Write-Output "WMI FilterToConsumerBinding 包含木马" } }
|
一键排查
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
| # 一键扫描木马自启动并输出清单
param(
[string]$malware = "C:\Users\Alice\AppData\Roaming\notepad_update.exe"
)
Write-Output "=== 开始扫描木马路径: $malware ==="
$outputFile = "$env:USERPROFILE\Desktop\MalwareScanResults.txt"
"" | Out-File $outputFile
# 注册表
$regPaths = @("HKCU:\Software\Microsoft\Windows\CurrentVersion\Run",
"HKCU:\Software\Microsoft\Windows\CurrentVersion\RunOnce",
"HKLM:\Software\Microsoft\Windows\CurrentVersion\Run")
foreach ($p in $regPaths) {
if (Test-Path $p) {
Get-ItemProperty -Path $p | ForEach-Object {
$_.PSObject.Properties | ForEach-Object {
if ($_.Value -like "*$malware*") {
$line = "注册表自启动: $p -> $($_.Name) = $($_.Value)"
Write-Output $line
$line | Out-File $outputFile -Append
}
}
}
}
}
# Userinit / Shell
$userinit = Get-ItemProperty -Path "HKLM:\Software\Microsoft\Windows NT\CurrentVersion\Winlogon" -Name Userinit
if ($userinit.Userinit -like "*$malware*") { $line = "Userinit 包含木马: $($userinit.Userinit)"; Write-Output $line; $line | Out-File $outputFile -Append }
$shell = Get-ItemProperty -Path "HKLM:\Software\Microsoft\Windows NT\CurrentVersion\Winlogon" -Name Shell
if ($shell.Shell -like "*$malware*") { $line = "Shell 包含木马: $($shell.Shell)"; Write-Output $line; $line | Out-File $outputFile -Append }
# 计划任务
schtasks /query /fo LIST /v | ForEach-Object {
if ($_ -match [regex]::Escape($malware)) { $line = "发现木马计划任务: $_"; Write-Output $line; $line | Out-File $outputFile -Append }
}
# 启动目录
$startupDirs = @("$env:APPDATA\Microsoft\Windows\Start Menu\Programs\Startup",
"C:\ProgramData\Microsoft\Windows\Start Menu\Programs\Startup")
foreach ($dir in $startupDirs) {
Get-ChildItem $dir -Recurse | ForEach-Object {
if ($_.FullName -like "*$malware*") { $line = "启动目录: $($_.FullName)"; Write-Output $line; $line | Out-File $outputFile -Append }
}
}
# 系统服务
Get-WmiObject win32_service | ForEach-Object {
if ($_.PathName -like "*$malware*") { $line = "发现木马服务: $($_.Name) -> $($_.PathName)"; Write-Output $line; $line | Out-File $outputFile -Append }
}
# WMI 持久化
Get-WmiObject -Namespace root\subscription -Class __EventConsumer | ForEach-Object {
if ($_.CommandLine -like "*$malware*") { $line = "WMI EventConsumer 包含木马: $($_.Name)"; Write-Output $line; $line | Out-File $outputFile -Append }
}
Get-WmiObject -Namespace root\subscription -Class __EventFilter | ForEach-Object {
if ($_.Query -like "*$malware*") { $line = "WMI EventFilter 包含木马: $($_.Name)"; Write-Output $line; $line | Out-File $outputFile -Append }
}
Get-WmiObject -Namespace root\subscription -Class __FilterToConsumerBinding | ForEach-Object {
if ($_.Consumer -like "*$malware*" -or $_.Filter -like "*$malware*") { $line = "WMI FilterToConsumerBinding 包含木马"; Write-Output $line; $line | Out-File $outputFile -Append }
}
Write-Output "=== 扫描完成,结果已输出到 $outputFile ==="
|





![[记录]尝试shiro有key无链利用,但失败](/img/c1/3.webp)

